Guardians of the Digital Realm: Navigating Cyber Threats Today

There is a large and delicate information exchange in this era of linked technologies and digital interdependence. Cybersecurity has grown into an essential problem as individuals, organizations, and government agencies struggle to reduce the threat of hostile actors trying to exploit weaknesses in digital systems. Considering they are continually developing, cyberthreats like ransomware-based sophisticated attacks, phishing campaigns, and sponsored by the government cyber-espionage pose an important danger. The cybersecurity community has created a number of methods to protect digital assets and maintain the integrity of online environments in response to these growing worries. This introduction explores the dynamic field of cybersecurity, highlighting various risks that infiltrate the digital sphere and illuminating the creative ways in which professionals counter and eliminate these threats.
The Situation of Cybersecurity
Here are a few significant facets of the cybersecurity environment:
New Technologies and Their Dangers
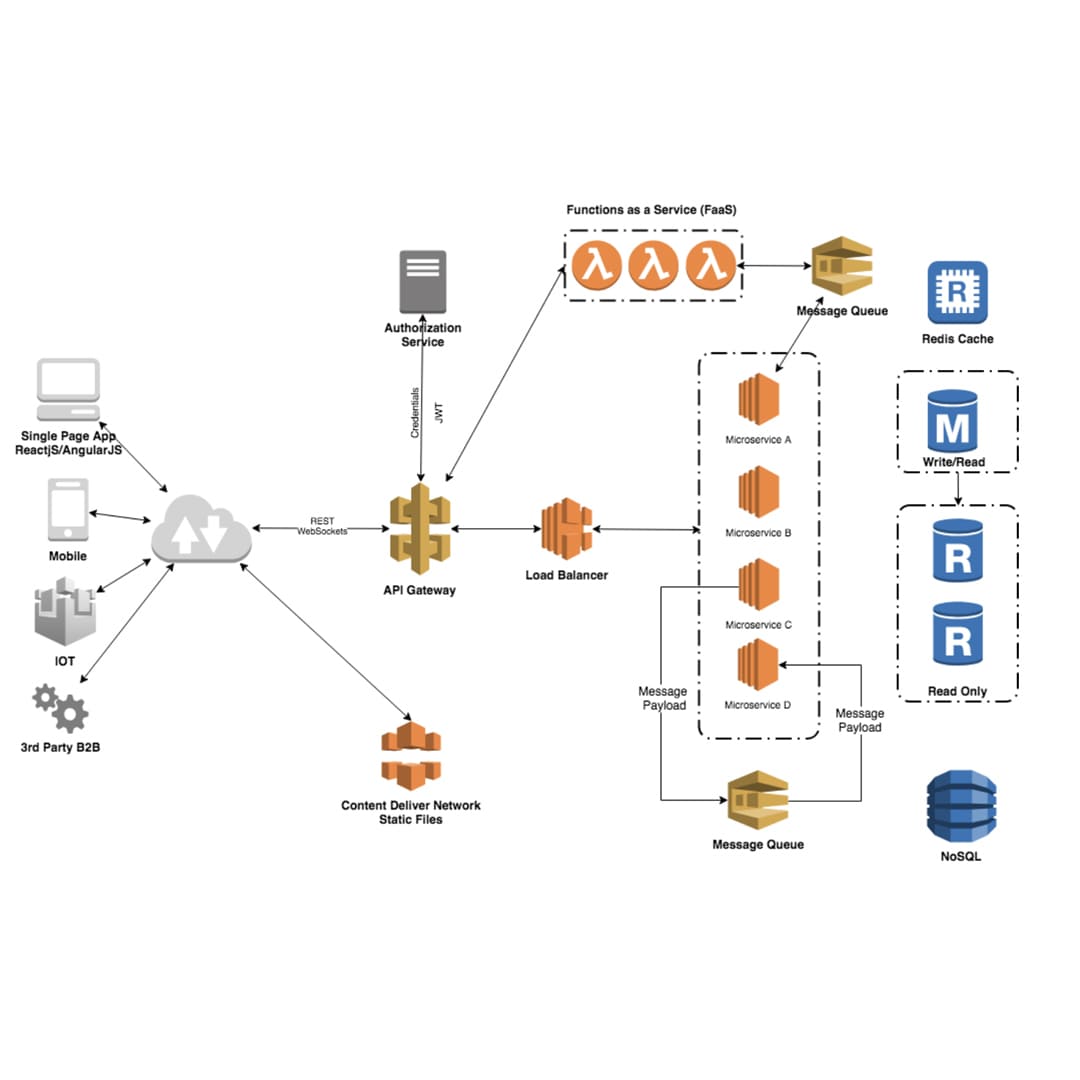
Cloud security: As cloud computing grows in popularity, situations involving cloud computing and data protection have grown more and more necessary.
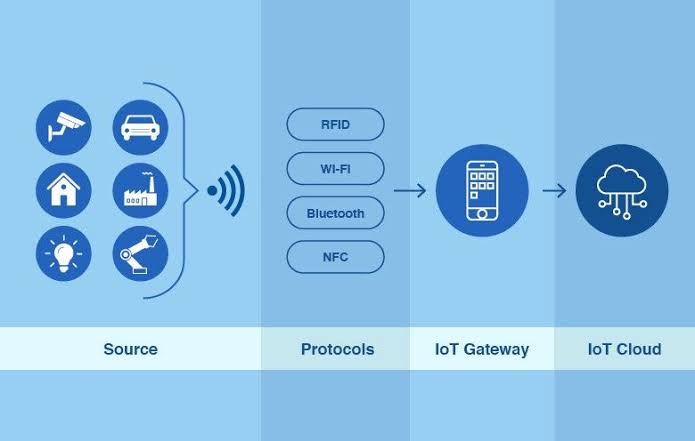
Internet of Things Security: As the assortment of IoT devices expands, so do the dangers to security that must be managed.
Whereas machine learning and artificial intelligence (AI) are both commonly employed in cybersecurity, they are often less hacker-friendly.
Cyberthreats
Ransomware attacks: These particular varieties of attacks encrypt sensitive information and demand ransom in exchange for its restoration. Ransomware represents a severe problem for individual users and organizations.
Phishing and social engineering: Cybercriminals typically employ social engineering measures in order to trick victims into clicking on potentially hazardous links or surrendering personal information.
Attacks on the supply chain: These entail identifying gaps in the system and using them to subtly breach companies.
Attacks by Nation-States: With the intention of attaining financial, political, or diplomatic objectives, there has been a notable increase in the quantity of nation-state cyberattacks in the recent past.
Remote Resilience: Best Practices for Cybersecurity in Remote Work
The zero trust security concept is being adopted by organizations. It is based on the notions that threats can come from both inside and outside the network, and that neither users nor systems should have confidence by default.
Endpoint Security: safeguarding individual devices (computers, mobile devices) against attacks from hackers is one of the primary branches of focus. the endpoint detection and response, or EDR, systems have become more and more prevalent.
Human Factor: Educating and raising awareness among employees about cybersecurity best practices is crucial as humans remain a weak link in security.
Cybersecurity Frameworks for Incident Response: It's important to create and carry out thorough incident administration plans.
Unlocking Cybersecurity: Ransomware Trends & Prevention
Concerning cybersecurity, ransomware constitutes a noteworthy and constantly developing threat. Here are a few ransomware patterns along with precautions to take:
Trends of Ransomware
Double Extortion: Hackers increasingly employ an approach known as "double extortion" with increasing frequency. In this technique, they encrypt the files belonging to the victim and acquire their personal information in the process. If they are not compensated for the ransom, they threaten to release the data openly.
Advanced Methods: In order to gain over conventional security measures, criminal organizations have developed increasingly sophisticated techniques and equipment in ransomware attackers.
Attacks that are highly targeted: Some ransomware attacks concentrate on particular companies or industries in an effort to worsen the harm they cause and maybe request the payment of a ransom. This is in opposition to widely spread operations.
Using "zero-day" vulnerabilities: By targeting security flaws that haven't been officially identified yet, cybercriminals can get unapproved access and download ransomware.
Threat-as-a-Service (PaaS): A portion of the ransom is given to criminal organizations who manage RaaS platforms, allowing people with less technological proficiency to commit ransomware violence.
Methods for Preventing Ransomware
Recovery and Backup: Make careful to often backup important data and to store the backups offline or in a secure location. Quick recovery is made possible without having to pay the ransom.
Update and Patch Systems: Update operating systems, software, and apps with the newest security updates to fix vulnerabilities that ransomware might exploit.
Division of a Network: Segment the network to prevent users from moving laterally within it. A compromised section can have a limited effect on the network as a whole.
User Education and Training: Educate staff members about methods of social engineering and phishing hazards and also a culture of cybersecurity awareness should be encouraged.
Email Security: Boost email security measures in order to filter out harmful applications and phishing interaction. In addition to other email authentication techniques, make use of Domain-based Message Authentication, Reporting, and Conformance too.
Access Control: Limited user rights and provide them access to only the resources they demand. Employ the concept of the least-privileged-party in order to reduce the prospective effects of a ransomware attack.
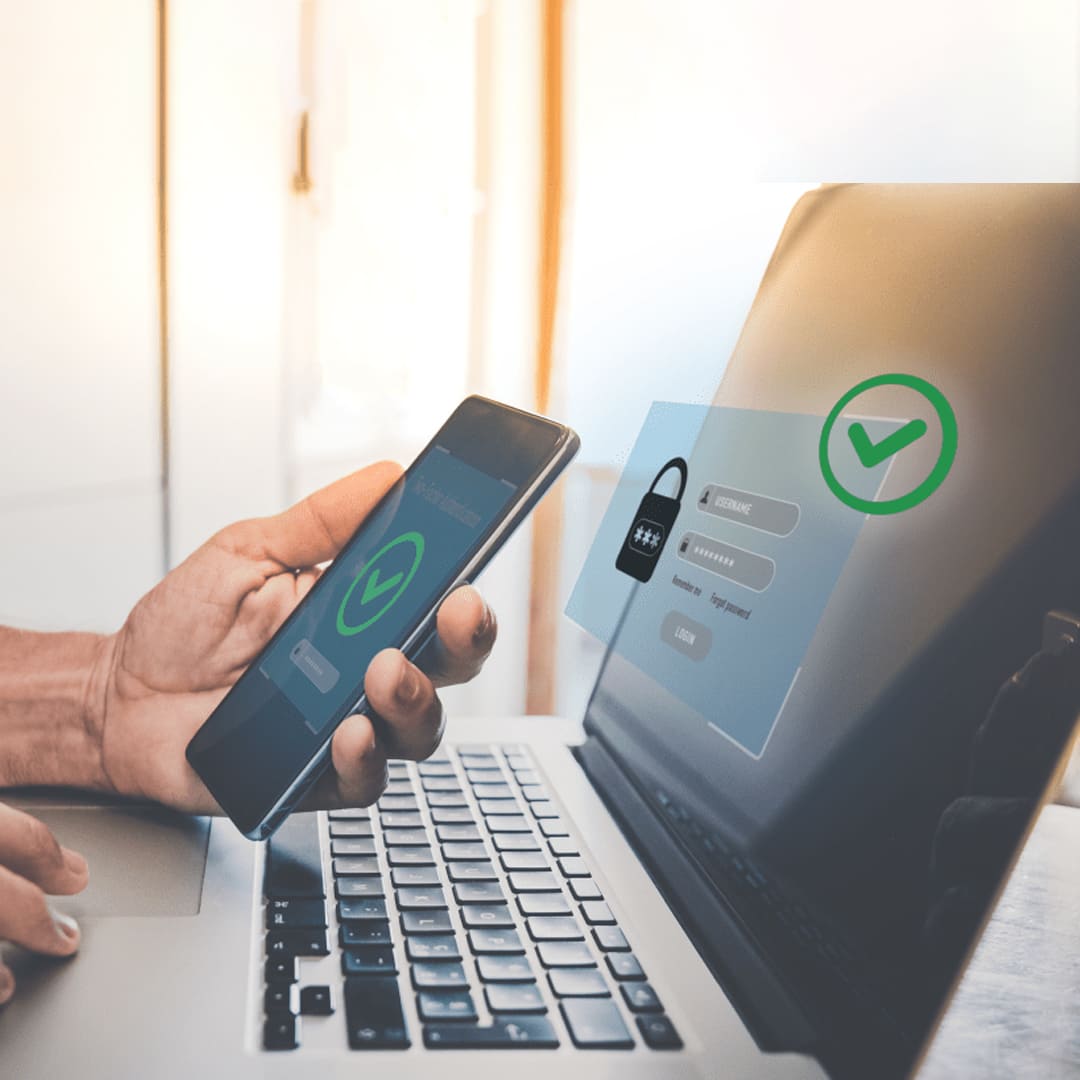
Strengthen security through the application of Multi-Factor Authentication (MFA) in order to prevent unauthorized people out of organizations that contain personally confidential data.
Incident Response Plan: Put into operation and regularly assess an incident response plan to guarantee that you can react immediately and effectively when faced with the possibility of a ransomware attack.
Security knowledge and Culture: It's essential to raise knowledge of safety concerns and create an effective cybersecurity ecosystem within the organization as a whole. Promote an anticipatory approach to security while encouraging the reporting of inappropriate behavior.
Involve Law Enforcement: Report ransomware circumstances to law enforcement organizations, and work with them to look into and maybe capture the offenders.
Because cyber dangers are constantly changing, it's critical to keep informed of emerging technologies and modify precautions for cybersecurity as necessary. Maintaining the never-ending battle against ransomware involves reviewing and improving prevention strategies on an ongoing schedule.
Zero-Day Heroes: Stay Ahead with Recent Cases and Protections
An attack that takes advantage of a software vulnerability that is unidentified to the program provider of services is commonly referred to as a "zero-day" exploit because this term indicates that there are no more days of protection guaranteed. Hackers and cybercriminals frequently employ these exploits numerous times to get into networks, steal information, or disseminate malware. Because they provide no time for resolving development and distribution before malicious people exploit them, zero-day vulnerabilities have become particularly concerning. New vulnerabilities have been identified over time, and specific instances involving zero-day exploits are vulnerable to quick adaptation. Organizations and software vendors actively work to identify and address these issues through patches and updates. Stay informed through reliable cybersecurity news sources for the latest developments.
Protections Against Zero-Day Exploits
Patch Management: To address recognized vulnerabilities, update and repair all operating systems, applications, and software on an ongoing basis. When a vulnerability has been identified, vendors frequently distribute remedies.
Segment your network: Segment your computer network to lessen the consequences of a possible compromise. One way to help contain the harm that occurs is to disconnect important systems from fewer important ones.
Application Whitelisting: Restrict the number of permitted apps that are permitted to run on a system by employing application whitelisting. This might prevent harmful or unapproved programs from functioning.
Behavioral Analysis: Implement solutions that employ behavioral analysis to detect anomalous patterns or activities on the network or within systems. Unusual behavior may be indicative of a zero-day exploit.
User education: Advise users of the potential hazards of opening attachments from unknown sources or clicking on suspicious websites. In order to prevent social engineering attacks that might utilize the advantage of zero-day vulnerabilities, knowledge among users is necessary.
Zero Trust Security Model: Adopt a zero-trust security framework in which there is no default degree of trust for any entity—inside as well as outside the network. Everyone requesting to access resources needs to provide verification, even if they have previously been linked to the network.
Vulnerability Management: To identify and eliminate possible holes in systems before hackers can exploit them, frequently execute penetration examinations and assessments of vulnerabilities.
Security Information and Event Management (SIEM): Collect and examine log data from multiple systems that are connected to the network employing SIEM solutions. This can help in early detection of unusual activities.
Cooperation and Information Sharing: Exchange information with pertinent government agencies, cybersecurity communities, and other entities. Early warnings concerning new hazards can be given by using this cooperative strategy.
Recall that correct application and ongoing oversight are necessary for protective measures to be effective. Having a thorough cybersecurity plan, updating software, and remaining watchful are crucial parts of defense against zero-day vulnerabilities. In addition, in the always changing field of cybersecurity, seeking advice from professionals in the field and remaining up to date on new threats are essential.
Guarding Your Digital Castle: The Power of Multi-Factor Authentication
Since employees are dispersed and work in many different kinds of environments, remote work introduces unique risks related to cybersecurity. Strong procedures for cybersecurity must be put in place with the objective to minimize risks and protect personally identifiable information. Considerations for cybersecurity in situations involving remote work are listed below:
Assure secure information transmission between their devices and the company network by mandating that staff members use virtual private networks (VPNs) to protect their online browsing activities. This minimizes the chance of a third party listening in on confidential data.
Multi-Factor Authentication (MFA): Encouraging the implementation of MFA, or multi-factor authentication, has significance when approving utilization of computer systems and applications used by businesses. By establishing another level of safeguarding on top of credentials, this reduces the likelihood of unauthorized access.
Secure Wi-Fi Connections: Encourage the use of encrypted with a password secure Wi-Fi networks among your employees. For essential professional reasons, stay away from public Wi-Fi. If you definitely need an additional layer of encryption, implement a VPN.
Frequent Software Updates and Patching: Ensure that personnel maintain the most appropriate security patches installed on their computer's operating system, software, and mobile applications. Updates on an ongoing schedule assist in addressing weaknesses that attackers potentially leverage.
Endpoint Protection: Confirm that endpoint protection software, such as antivirus and anti-malware applications is installed on every gadget employed for work. Update and check devices for risks on a regular basis.
Collaboration Tools That Are Secure: Make certain that the instruments you use are secure by thoughtfully choosing and implementing them. Use end-to-end encryption for communication and enable security settings to control access.
Secure Password Guidelines: Encourage the establishment of strong, distinctive passwords for each and every account. Promote the application of password managers as an encrypted means to deal with and store sophisticated passwords.
Employee Awareness and Training: Educate workers who work remotely on cybersecurity on a regular schedule. Include subjects like the use of social engineering, phishing awareness, and the latest techniques for safeguarding their work environment.
Secure File Sharing: Enable access controls and encryption when establishing secure file-sharing structures in order to protect confidential documents when they are circulated among members of the team.
Remote Device Management: Employ remote device administration technologies to monitor and manage your devices from distant locations. This includes having the capacity of erasing data from abandoned or stolen devices.
In conclusion, it is important that all stakeholders—individuals, businesses, and governmental entities—respond adaptably and constructively to the continually shifting and persistent danger that is the cybersecurity landscape. In an economy that continues to become ever more interconnected by the day, it is fundamental that we implement strong cybersecurity safeguards. Malevolent actors' unwavering ingenuity and acuity necessitate an ongoing drive to upgrading cybersecurity systems. Cooperation, communication of data, and investment in cutting edge technology are vital for stakeholders to stay ahead of the ever-evolving threat circumstance. By embracing revolutionary innovations like artificial intelligence that recognize risks, increasing user education, and developing a cyber resilient culture, we can collaboratively enhance our digital ecosystems. The creation of practical cybersecurity solutions is still necessary to maintain our privacy, national security, and economic stability in a world growing more interconnected by the day.
Recent Stories
500k Customer Have
Build a stunning site today.
We help our clients succeed by creating brand identities.
Get a Quote