Strategies for Regular Security Audits and Updates

Any successful cybersecurity plan must include regular security assessments and updates given the modern digital environment. Organizations need to be proactive in evaluating and strengthening their safety protocols to protect sensitive data and sustain their operational sustainability, given the ever-changing threat landscape and the increasing complexity of cyberattacks. Dependence on reactive safety procedures alone is insufficient in this day of rapid technological innovation. It is critical that you employ proactive strategies to carry out regular security audits and updates. In order to operate effectively and minimize possible security breaches, businesses can detect vulnerabilities, assess risks, and begin implementing appropriate patches and enhancements by doing accordingly. The context for understanding the significance of frequently received security audits and modifications to improve comprehensive security posture is given in the first sentence of this section.
The Value of Updates and Audits for Security
Maintaining the security and reliability of any system, network, or program that uses software needs regular security audits and upgrades. This is the reason why they have significance:
- Finding Vulnerabilities: Audits for security entail comprehensive reviews of networks, applications, and devices to find holes or vulnerabilities that an intruder could attack. Through these inspections, security professionals can identify potential dangers and possibilities that might otherwise go unnoticed.
- Preventing Data Breaches: Regular security audits contribute to identifying and correcting security flaws before malicious individuals take pleasure in them. By maintaining ahead of any dangers, organizations can significantly decrease the likelihood of data breaches and subsequent financial and damage to their reputations.
- Compliance rules: Numerous sectors and regulatory agencies require companies to perform periodic security assessments for the purpose to ensure that they comply with specific legislation and regulations. There could possibly be harsh punishments and legal ramifications for breaking those regulations.
- Preserving Customer Trust: Frequent security audits show stakeholders and customers that a company takes data security seriously. This contributes to the development of trust and confidence in the company's security measures, which is necessary to keep customers satisfied and loyal.
- Preventing Emerging dangers: As attackers create new methods and exploits to get past security measures, cyber dangers are always changing. Organizations that conduct regular security audits are better able to proactively apply security measures to limit risks by staying updated about emerging threats and vulnerabilities.
- Enhancing Security Posture: Audits for security not only find weaknesses but also provide best practices as well as suggestions that can improve an organization's security in general posture. By implementing the aforementioned recommendations into practice, safety safeguards become more effective and the probability of achieving successful cyberattacks is minimized.
- Maintaining Software Integrity: In order to fix known vulnerabilities as well as fix defects in programs that run on computers, regular patches and updates to the software are required. Malicious individuals may target systems that have not received timely updates. By staying current with software upgrades, organizations may reduce the risk of security breaches and ensure the integrity of their computer network.
Regular security audits offer several key benefits:
Regular security audits offer several key benefits:
- Vulnerability Identification: In order to find holes and flaws in systems, networks, and applications, security audits are helpful. Conducting routine audits can help organizations stop hostile actors from exploiting possible security flaws.
- Hazard reduction: By identifying gaps and vulnerabilities and putting the appropriate safeguards in place, organizations can lower risks and strengthen their security posture. This could involve installing security controls, updating software, or enhancing security policies and procedures.
- Assurance of Compliance: Organizations must adhere to a number of security standards and laws, as mandated by numerous industries and legal frameworks. To guarantee adherence to these regulations and lower the possibility of fines and legal repercussions, regular security audits are suggested.
- An organization's ability to respond to security crises and prepare for them can be evaluated through regular security audits, which can lead to an improvement in emergency preparedness. By identifying weaknesses in an organization's incident response procedures, security breaches may be lessened and preparedness increased.
- Enhanced Stakeholder Trust: Partners, clients, and stakeholders can all feel more confident in one another when audits are conducted consistently and show a commitment to security. Proof of the company's proactive security planning and careful attention to sensitive data protection.
- Cost Savings: By preventing expensive safety incidents and subsequent damages, firms may ultimately conserve money by aggressively recognizing and fixing security weaknesses through periodic inspections. A successful cyberattack could result in damages in terms of both money and reputation, which can be prevented by making proactive security expenditures.
- Constant Improvement: Since security constitutes an ongoing procedure, frequent audits offer opportunities for continuous improvement. Organizations can further develop their security plans, modify regulations and processes, and improve employee awareness about safety with the assistance of the audit findings.
In conclusion, frequent security audits have several advantages, such as enhanced risk management, assurance of compliance, readiness for incident response, confidence among stakeholders, financial savings, and ongoing security practice improvement.
Techniques for Performing Frequent Security Audits and Updates
To maintain efficacy and efficiency, conducting frequent security assessments and updates calls for a thorough, methodical approach. Here are a few methods for carrying them out:
- Clearly State Your Goals: Clearly state your goals for the security audits and upgrades, such as finding vulnerabilities, making sure rules are followed, or enhancing overall security posture. Clear objectives help focus efforts and resources effectively.
- Schedule: Organize upgrades and security audits into a regular regimen. Depending on the risk profile of the company, industry laws, and operational requirements, this could be completed annually, semi-annually, or frequently.
- Determine Any Possible Vulnerabilities Streamline and Ensure Efficiency in the Audit Process: Utilize solutions for automatic security scanning and monitoring. These tools can help identify security issues across systems, networks, and applications more quickly than manual methods.
- Engage Security Experts: Consider involving external security experts or consultants to conduct independent security audits. Their expertise and fresh perspective can uncover vulnerabilities that may be overlooked internally. Additionally, they can provide valuable insights and recommendations for improving security.
- Examine Security Policies and processes: Ensure that security procedures, regulations, and guidelines are regularly examined and revised to reflect new dangers and standards of excellence. This covers recommendations for employee instruction, incident response, restriction of access, as well as information protection.
- Test Incident Response Plans: Evaluate the efficacy of incident response plans in managing security incidents as part of security audits. To assess how prepared the company is to handle different kinds of security threats, run simulated drills.
- Keep an eye out for Emerging Risks: Keep up with the latest cybersecurity threats and weaknesses that could affect the systems and programs your company employs. To remain ahead of developing dangers, cooperate with colleagues in the field, take part in forums where information is shared, and subscribe to threat intelligence feeds.
- Strong patch management protocols will enable the timely distribution of security updates and patches for firmware, operating systems, and software. Prioritize patching according to severity and regularly check systems for vulnerabilities and missing fixes.
- Employee Education: Make sure staff members are regularly trained in security awareness so they can identify security risks, comprehend security guidelines, and follow recommended methods for safeguarding confidential data. Strong security posture maintenance depends heavily on knowledgeable staff.
- Remedial Plans and Audit results: Document audit results, including vulnerabilities and compliance gaps discovered, along with recommended remedial actions. Create precise repair plans with deadlines and roles allocated to pertinent parties.
- Monitor and Assess Developments: Stay informed about the efficiency with which security updates are being implemented and the resolution of audit findings. To assess the effectiveness of safety procedures and their evolution over time, track measurements and key performance indicators (KPIs).
Organizations are able to enhance their security posture, minimize the likelihood of security breaches and regulatory infractions, and conduct routine security inspections and updates effectively by putting the aforementioned methods into action.
Top Techniques for Keeping a Secure Environment
Safeguarding confidential information, preventing cyberattacks, and guaranteeing company continuity all depend on maintaining a secure environment. The following are recommended procedures for keeping an environment safe:
- Put a Layered Security Approach into Practice: Install several tiers of security measures, such as endpoint security solutions, network firewalls, intrusion detection/prevention systems, antivirus programs, and safe setups for hardware and software.
- It is recommended to apply system security patches and updates on a regular basis: Update all firmware, applications, and devices with the most recent security updates. Attackers routinely gain unauthorized access to systems simply by taking advantage of flaws in outdated application sources.
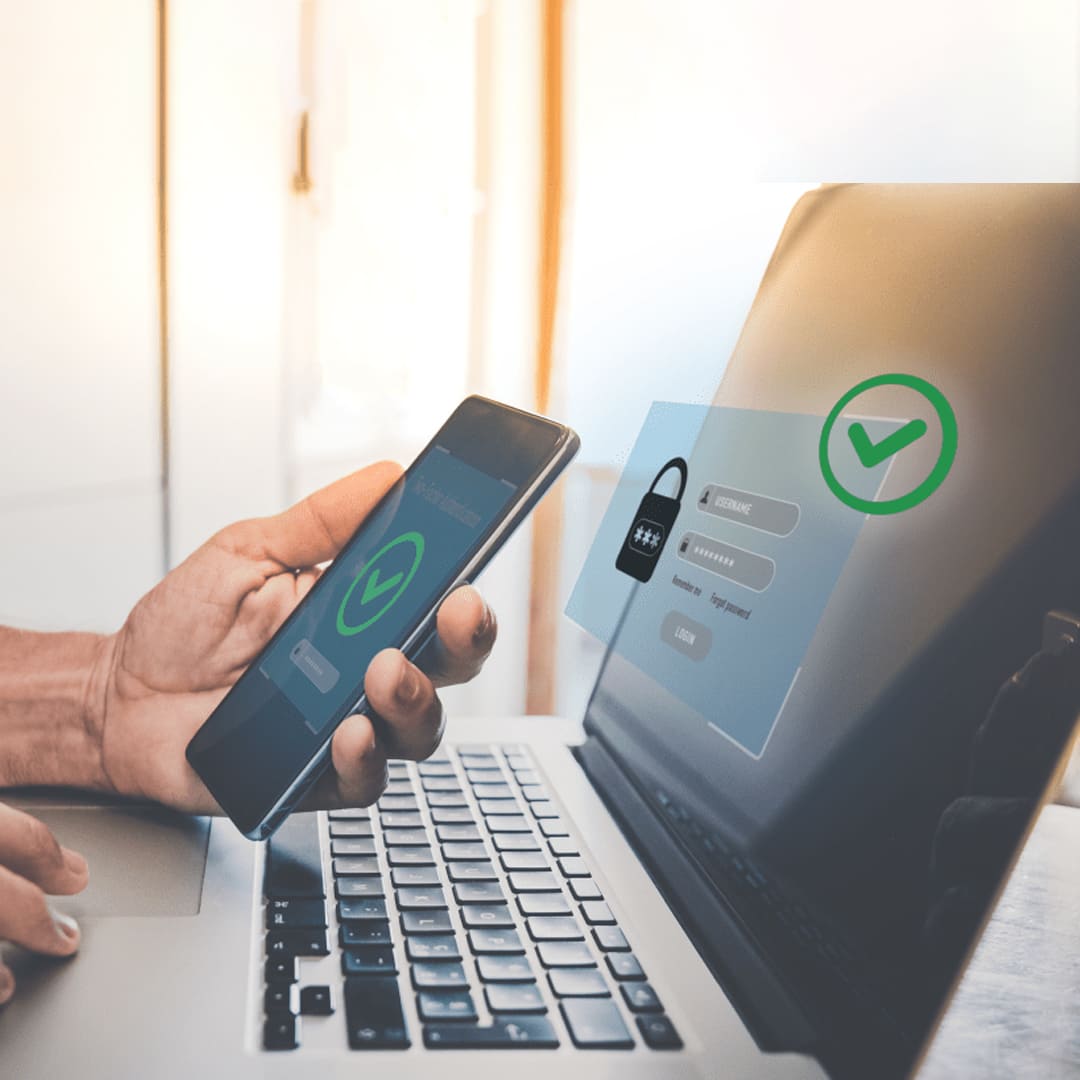
- Use the least privileged access principles in order to limit access to highly confidential information and vital infrastructure to those with authorization only. Establish Robust Access Controls. Access security can be increased by utilizing robust authentication methods like multi-factor authentication (MFA).
- Encrypt Sensitive Data: To ensure its security during storage and transmission, encrypt sensitive data. For data transmission over networks, use secure communication protocols and encrypt data stored on servers, databases, and storage devices.
- Track and Analyze Security Events: Install trustworthy logging and monitoring tools to keep an eye out for suspicious activity and security events on different systems and networks. Correlate and examine log data using security information and event management systems to identify any security incidents.
- Create Incident Response processes: To address security incidents, breaches, and data breaches efficiently, create and maintain thorough incident response processes. For managing security events, clearly establish roles, duties, and escalation protocols.
- Employee Education and Preparation: To keep staff members up to date on security best practices, phishing dangers, social engineering techniques, and the need of securing sensitive data, they should provide ongoing security awareness training. Insist that the company foster a security-focused culture.
- Put in place secure remote access solutions if employees are working remotely or accessing company resources from external networks. Enforce strong authentication and encryption for remote connections.
- Backup Your Data Often: Make sure your data is available and intact in case of ransomware attacks, data loss, or other emergencies. Maintain the safety of backups and periodically test restoration processes to ensure their efficacy.
- Stay Up to Date on Emerging Threats: Keep abreast of the most recent cybersecurity risks, weaknesses, and attack patterns that are relevant to your company's sector and technological environment. Remain informed by following threat intelligence streams, industry forums, and security warnings.
- Enforce Security rules and processes: Create and implement security rules, guidelines, and processes that control software usage, data handling, password management, and remote access, as well as the appropriate use of IT resources. Review and update rules frequently to take into account modifications to laws and technology.
Organizations may preserve their assets, reputation, and consumer trust, as well as build a strong security posture and reduce the risk of security breaches, by adhering to these best practices.
Conclusively, given the contemporary digital landscape, it is imperative to institute procedures for periodic security assessments and upgrades. Organizations can successfully reduce the risk of data breaches and system intrusions by avoiding potential cyber threats and selecting preventative measures over reactive ones. Regular upgrades guarantee that systems continue to be secure against new threats, and thorough security audits can find and fix weaknesses. The culture of continuous improvement and focus on cybersecurity also support a robust and flexible approach to safeguarding sensitive data and maintaining operational continuity. Consequently, companies can strengthen their defenses and successfully mitigate the constantly changing threats provided by cyber adversaries by implementing frequent security audits and updates into their cybersecurity operations.
Recent Stories
500k Customer Have
Build a stunning site today.
We help our clients succeed by creating brand identities.
Get a Quote