Guarding Your Digital Castle: The Power of Multi-Factor Authentication
Nowadays, with technological developments and networked technology taking place at the forefront, safeguarding personal information is essential. There is an increased likelihood of unwanted access and security breaches as both individuals and companies depend more on digital platforms for communication, trade, and data storage. Due to these constantly developing dangers, the security ecosystem increasingly depends more and more on multi-factor authentication, or MFA. By requesting users to independently confirm their personal information through a variety of means, multi-factor authentication (MFA) offers a further degree of security on top of the protection of their passwords. In the contemporary digital landscape, multi-factor authentication (MFA) is a vital component since it increases security and lowers the dangers concerned with single-factor authentication. This presentation highlights the significance of multi-factor authentication and how it increases cybersecurity across multiple industries.
An Extensive Guide to Two-Factor Verification
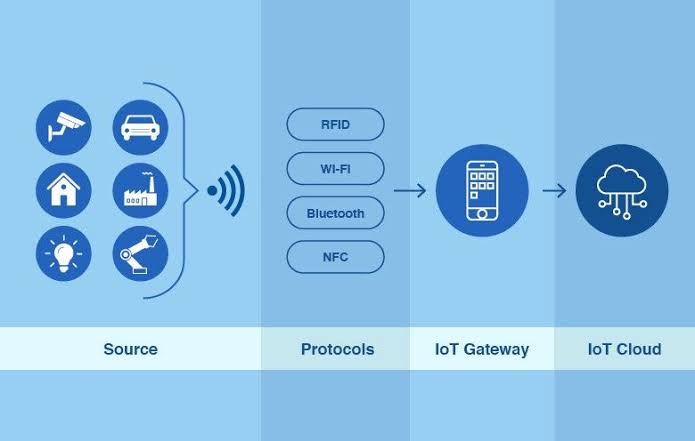
Before granting users access to a system, program, account, or other resource, a preventive measure known as multi-factor authentication, or MFA, requires them to present numerous kinds of identity verification. MFA attempts to improve security by providing an extra layer of protection on top of the conventional login and password setup. The incorporation of extra factors improves the difficulty for unregistered individuals to access the computer system, even in the unlikely circumstance that one factor—such as a password—is discovered. The variables that follow are common multi-factor authentication aspects:
- Knowledge Factor (Something You Know): This is typically a password or PIN that only the user should know. It's the most common form of authentication but is often considered the weakest on its own.
- Possession Factor (Something You Have): This involves a physical device or token that the user possesses. Common examples include:
- One-Time Password (OTP) Generators: These electronic devices or applications generate short numerical codes that users have to enter when they want to get logged in.
- Smart Cards: Laminated cards with embedded semiconductors that hold confidential information for authentication.
- Biometric Factor (Something You Are): This encompasses an individual's distinctive characteristics, either physical or behavioral. Common biometric factors include:
- Fingerprints: Scanning a user's fingerprint for identification.
- Retina or Iris Scans: Analyzing the unique patterns in the eyes.
- Facial Recognition: Analyzing aspects of a person's face for identifying identity.
Voice recognition is a method of examining every human being's distinctive voice characteristics.
The goal is to independently verify the user's recognition through the integration of these several variables. One typical solution could be to enter both a temporary code from a mobile app (possession factor) and a username and password (knowledge factor).
Two-factor authentication's advantages
- Enhanced Security: MFA substantially improves security by making it impossible for those without authorization to gain access.
- Diminished Danger of Unauthorized Entry: In the unlikely scenario that a single factor has been compromised, the attacker would nevertheless need access from the remainder of the factor or circumstances.
- User Verification: You can be more confident that the person who's trying to access an application or account is an authorized member through setting multi-factor authentication (MFA) into existence.
Though MFA dramatically improves security, it's necessary to remember that no system is completely secure at all times. A comprehensive security strategy also needs to involve instruction for users, monitoring, and periodic updates to the security software.
The Drawbacks of Using a Single Factor for Authentication
There are several weaknesses in security connected to single-factor authentication (SFA), which usually necessitate a single form of identity, like a username or password or PIN. Those that follow are some of the main vulnerabilities in single-factor authentication:
Password Vulnerabilities:
- Weak Passwords: weak or easy passwords that are easy to be guessed or even cracked are often utilized by users.
- Reusing passwords: A lot of distinct individuals use the exact same password across multiple accounts, which increases the possibility of vulnerability in the event that one account is hacked.
- Storage of credentials: Insecure password storage renders credentials susceptible to exploitation in breaches of information.
Phishing Attacks:
- Social Engineering: To mislead users into divulging information about themselves, attackers may send fraudulent emails or texts, or fake websites.
- Credential Harvesting: fraudulent attempts may result in the collection of login information, which could provide unwanted utilization of accounts belonging to users.
- Brute Force Attacks: In an effort to meticulously guess passwords, attackers try an assortment of combinations until they come across the most suitable one. Attacks involving brute force are more common with low or straightforward passwords.
- Credential Stuffing: Attackers use stolen username-password pairs from one service to gain unauthorized access to other accounts where users have reused the same credentials.
- Keylogging: Malevolent software or hardware that records keystrokes has the ability to intercept usernames and passwords as they are input.
- Lack of user authentication: After a password has been compromised, it will be simpler for unauthorized people to gain access because SFA only requires the login and password.
- Lost or Stolen Devices: If a physical device, such as an identification document or smart card, needs to be used for single-factor authentication and it goes missing or is stolen, a person who is not authorized may be able to gain entry to the system.
- Unable to Verify User Identity: It is impossible to verify that the individual entering the password is actually the account owner due to the lack of additional information.
- Limited Security in High-Risk Environments: In circumstances where there is a substantial possibility for unwanted access, such obtaining access to sensitive systems or performing transactions involving money, single-factor authentication may fail to provide adequate safeguards.
It is recommended to implement multi-factor authentication (MFA) for the purpose to significantly enhance your security posture by adding extra phases to verification given the existence of these vulnerabilities. Many of the potential risks connected to employing merely a single factor for authentication have been mitigated by MFA.
The advantages of two-factor authentication
The security of personally identifiable information, systems, and accounts has been substantially enhanced by the benefits that Multi-Factor Authentication (MFA) provides. The ones that follow are some of the primary advantages of using MFA:
- Enhanced Security: MFA adds an additional degree of security to password protection, making it impossible for unauthorized users to log in. The additional variables operate as a supplementary barrier, even in the unlikely scenario that one is damaged.
- Decreased Risk of Unauthorized Access: There is a substantial reduction in the risk of unauthorized entry when numerous factors need to be present for authentication. This is particularly significant for protecting sensitive information and critical infrastructure.
- Protection Against Credential Theft: By using strategies like tracking keystrokes and phishing, MFA may decrease the effects of the theft of credentials. These further factors provide a further measure of security, even in the unlikely circumstance that passwords are compromised.
- Regulation Compliance: The implementation of multi-factor authentication as a component of security precautions for information is either encouraged or required by an assortment of regulatory standards and requirements for compliance, including GDPR, PCI DSS, and HIPAA.
- User Verification: MFA offers an additional level of assurance when it has to do with confirming an individual's identity. It guarantees that the individual who is gaining login to the account is legitimate and not a person whose access is not accepted.
- Flexibility to Select Various Factors: Multi-factor authentication (MFA) gives businesses the option of choosing from a range of variables that include the ownership (like tokens or mobile devices), information (like passwords), and fingerprints.
- Risk Mitigation Associated with Passwords: MFA assists in minimizing the risks that are caused by weak passwords, reusing login credentials, and attacks based on brute force through decreasing dependency on passwords alone.
- User-Friendly Authentication: When compared to more standard methods, some MFA types—like biometric scans or push notifications—offer a more straightforward to use approach. As a result, users may be more pleased with the process of authentication overall.
- Real-time notifications and monitoring: MFA systems are frequently equipped with the capacity to send as well as receive notifications instantaneously. Businesses have the ability to quickly recognize and respond to unexpected login attempts with the help of this.
- Enhanced Trust in Online Transactions: By introducing an extra degree of safeguarding to online transactions, multi-factor authentication (MFA) improves users' confidence in the dependable nature of the platform while decreasing the likelihood of transactions that are forged.
- Remote Access Security: Multi-factor authentication (MFA) has become ever increasingly important for protecting sensitive data and network connections for businesses from a range of locations as remote work grows more and more prevalent.
- Cost-effective Security Measure: The long-term benefits of implementing MFA, such as enhanced safety and a lower chance of data breaches, could compensate for the expenses that accompany security-related instances. However, there may be certain installation fees beginning.
Organizations are able to construct a strong authentication architecture that significantly strengthens overall security measures by combining several distinct components.
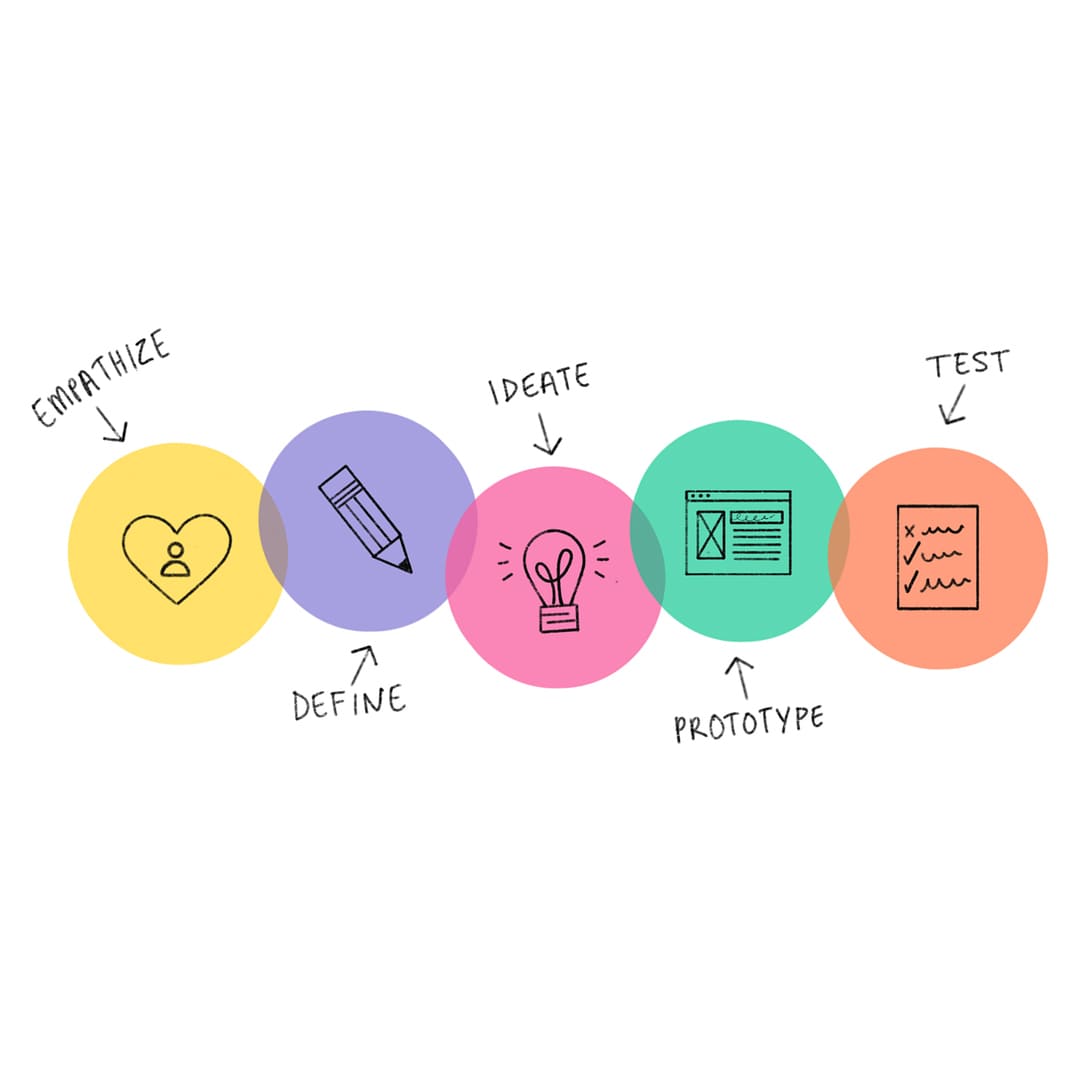
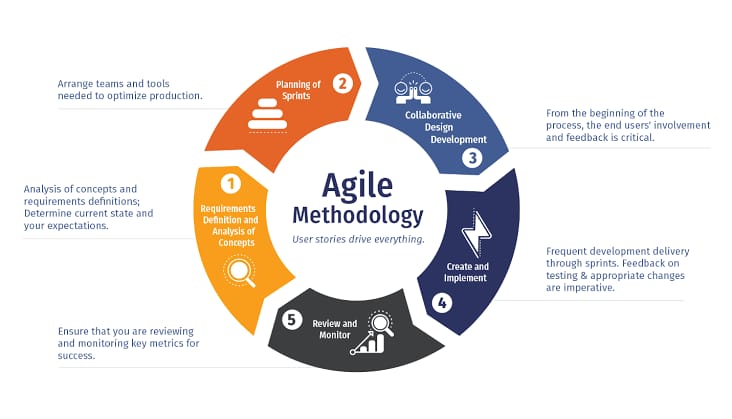
Key Ideas in Multi-Factor Authentication
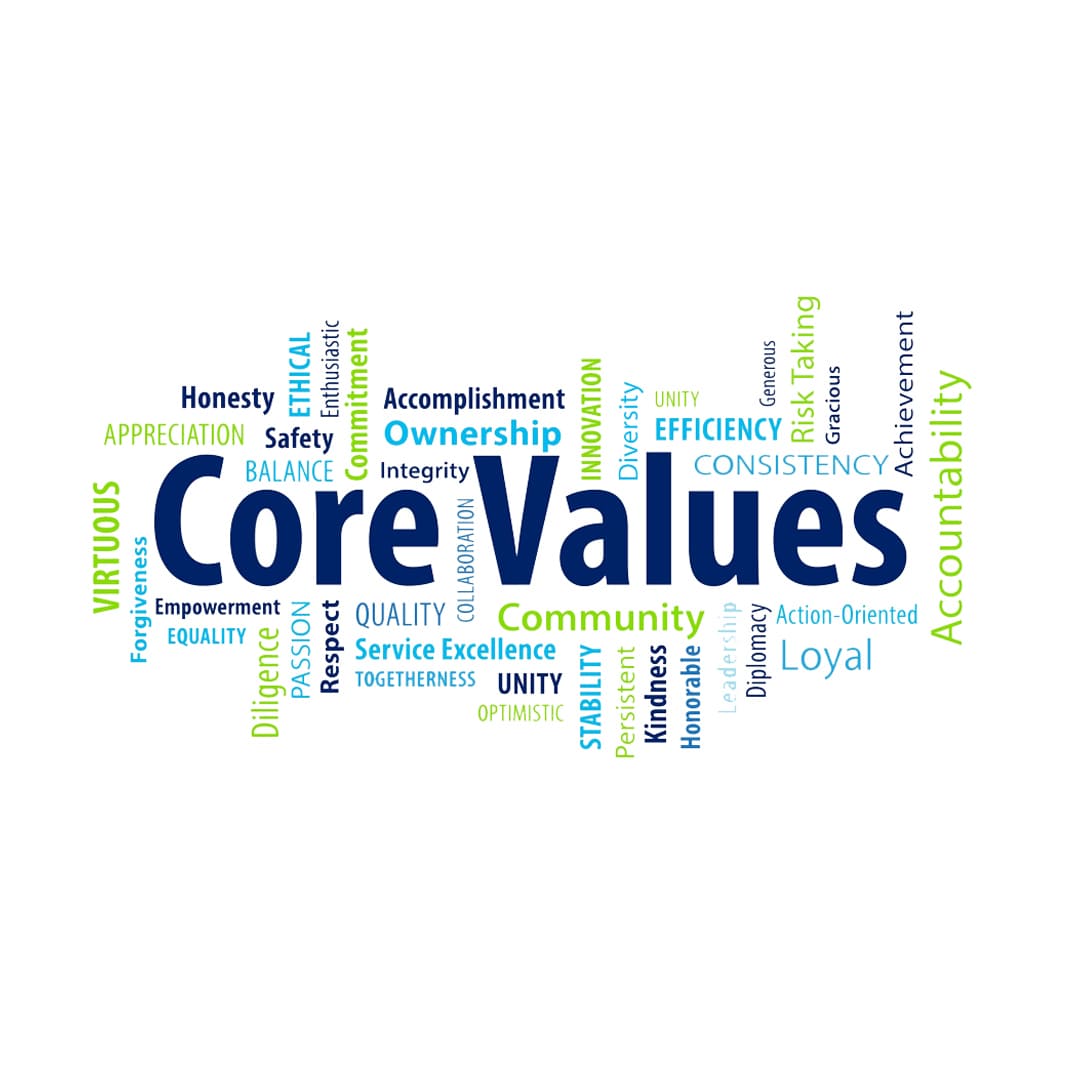
Multi-Factor Authentication (MFA) has to be established according to certain basic principles in order to achieve the greatest degree of safety. These principles help establish a strong and reliable authentication process. Here are some key principles of MFA:
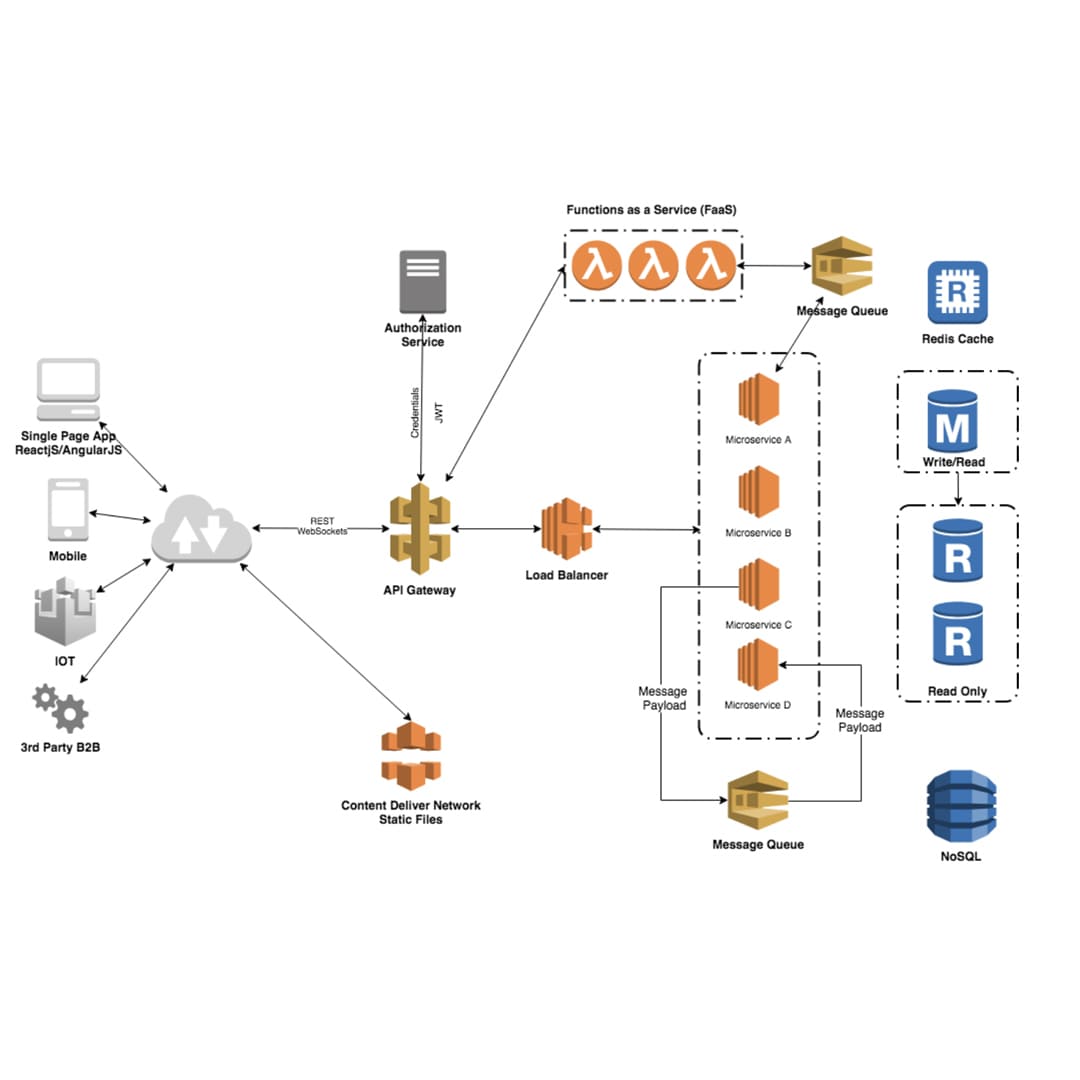
- Employ Multiple Authentication Factors: Multi-factor authentication (MFA) necessitates a combination of two or more authentication factors, which are typically chosen from three categories: something that you possess (like a mobile device or token), something you're aware of (like a password), and something that is unique to you (like biometric data). The combination of factors adds layers of security.
- Factor Independence: Each authentication factor should be independent of the others. It ought not to be simpler to compromise a single component than another while another is exposed. For instance, if physical device possession is also required, then unauthorized access should not be feasible through the theft of passwords.
- Layered Security: Multifactor authentication functions best when utilized alongside additional safety measures. It needs to be included in a multilayered security plan that also includes firewalls, encryption connections, and periodic security assessments.
- Flexibility and Adaptability: Multi-factor authentication (MFA) systems must be responsive to a variety of authentication elements and sufficiently adaptable to keep pace with the times in order to fulfill changing requirements for security. As a result of its flexibility, companies are able to select the components that best fit their particular demands.
- User-Friendly Implementation: In an attempt to promote adoption, MFA frameworks should be implemented with ease of use in mind. It has to be essential for achieving a balance between safety and convenience in order to prevent aggravating users and guarantee that MFA will be supported by the user population.
- danger-Based Authentication: In order to assess the degree of danger associated with an individual login attempt, organizations ought to implement hazard-based authentication. The authentication standards can be dynamically adjusted by the system based on risk-related factors like device, location, or behavior of users.
- Secure Credential Storage and Transmission: Passwords and biometric details should be securely preserved and communicated, in addition to all other authentication credentials. This is helpful in preventing personally identifiable information from being obtained without authorisation during the process of authentication.
- Monitoring and Logging: By putting effective monitoring and logging mechanisms in place, organizations can keep track of authentication events, detect irregularities, and promptly address any issues related to security. Alerts provided in real time can be extremely beneficial in spotting suspicious behavior.
- Constant Monitoring and Updates: Keep an eye on the manner in which MFA systems are performing and update them whenever necessary to fix vulnerabilities or emerging threats. This includes keeping up with developing authentication technologies as well as business requirements.
- Standards and Regulation Compliance: Ensure that MFA installations adhere to relevant industry standards and legal requirements. Compliance enables organizations to uphold their legal responsibilities and contribute to a healthier environment.
- Instruction and training: providing users with understanding on the importance of multi-factor authentication (MFA), how to utilize it, and how to recognize attempts at phishing. Every safety measure's effectiveness depends upon user awareness.
- Balanced User Experience: Aim for a user experience that strikes a balance between simplicity and trustworthiness. If you want to adjust the security level in accordance with the conditions accompanying the login attempt, consider implementing adaptive methods of authentication.
Organizations can put together an effective multi-factor authentication mechanism that enhances overall security and aids in repelling a range of assaults by following the aforementioned recommendations.
Implementation Challenges and Solutions
Here are common implementation challenges and potential solutions:
User Resistance:
- Challenge: Due to perceived level of complexity or annoyance, users might be hesitant toward accepting MFA.
- Solution: Clearly communicate the advantages of multi-factor authentication, provide simple to operate ways for identifying users, and conduct training sessions to educate users about the significance and suitable implementation of MFA.
Integration Issues:
- Challenge: It can be challenging to combine MFA with third-party services, applications, or present-day systems.
- Solution: For straightforward integration, use MFA solutions that embrace standards from the industry like OAuth and SAML. Make use of IAM (identity and access management) platforms, cooperate closely with vendors, and optimize the use of APIs to make collaboration simpler.
Cost Concerns:
- Challenge: The beginning and ongoing expenses linked to putting MFA into action and keeping it up to this point can cause concern organizations.
- Solution: To show the potential savings from reduced security incidents, do an evaluation of costs and benefits. For reduced infrastructure costs, explore reasonably priced multi-factor authentication (MFA) alternatives and consider cloud-based MFA solutions.
User Experience and Usability:
- Challenge: Poorly designed or cumbersome MFA methods can impact user experience.
- Solution: Go for straightforward authentication techniques like fingerprints or push alerts. Seek for a balance between accessibility and security, and to make modifications, get input from customers.
Phishing and Social Engineering:
- Challenge: Phishing attacks may still trick users into providing their MFA credentials.
- Solution: Educate users about phishing risks and how to recognize phishing attempts. Use adaptive authentication in order and anti-phishing techniques, such email filtering, to spot suspicious login attempts.
Device Compatibility:
- Challenge: Ensuring MFA works seamlessly across various devices and platforms can be challenging.
Solution: Choose MFA solutions that support a wide range of devices and platforms. Test MFA implementations on different devices and operating systems to ensure compatibility.
Lack of Standardization:
- Challenge: Lack of standardization may result in interoperability issues between different MFA solutions.
- Solution: Choose MFA solutions that adhere to widely accepted standards to ensure compatibility. Favor solutions that support protocols like FIDO2 for hardware-based authentication.
Issues with accessibility:
- Challenge: Users who are blind or visually impaired may have problems with accessibility when using some MFA approaches, such as fingerprints.
- Solution: Make sure MFA solutions conform to accessibility requirements and offer alternative authentication methods. Consider options like one-time codes or hardware tokens for users with specific accessibility needs.
Forgotten or Lost Devices:
- Challenge: Users may forget or lose devices used for MFA, causing access issues.
- Solution: Use backup methods for authentication (such backup codes) and give consumers an easy-to-follow methodology for replacing or retrieving lost devices. Educate users of the value of maintaining MFA devices protected.
Remote Resilience: Best Practices for Cybersecurity in Remote Work
To keep remote work environments safe, best practices must be implemented into action. For remote work, consider implementing the following cybersecurity suggested practices:
- Encrypted and secure Wi-Fi networks ought to be used by staff members. Stay away from public Wi-Fi for critical company-related tasks, and make sure the usernames and passwords on your home Wi-Fi connections are reliable and unique.
- Use multi-factor authentication (MFA) to provide user accounts a further layer of security. This minimizes the possibility of unwanted access regardless of the unlikely circumstance that login credentials are compromised.
- The installation and maintenance of anti-virus and anti-malware software on each gadget is safeguarding the endpoint. Scan devices frequently for potential hazards as well as making sure firewalls are used in order to avoid unwanted activity.
- Device Security: Put privacy settings in place for all of your technological gadgets, such as computers, tablets, and smartphones. This encompasses encryption, periodic software updates, as well as safe PINs or passwords for electronics.
- Employee Education and Awareness: To keep staff members informed about the newest dangers, phishing schemes, and security best practices for remote work, offer continuous cybersecurity training. Promote a security-conscious culture.
- Frequent Software Updates: Make sure that the most recent security patches are applied to all software, including operating systems, antivirus software, and apps. Software that is outdated may be open to hacking.
- Data Encryption: Promote the usage of encryption for private information while it's in storage and during transmission. This makes sure that even if data is intercepted, it can't be decrypted without the right keys.
- Security measures for the Remote Desktop Protocol (RDP) include robust authentication, encryption, and routine activity monitoring to spot any unusual activity. Consider using Virtual Private Network (VPN) connections for additional security.
- Data Backup and Recovery: Make sure that employees understand how to regularly backup the information they work with and put regular data backup adheres into place. In the event of an unanticipated event, develop a thorough data recovery process that will reduce data loss.
- To guarantee that employees are only allowed to use the resources that are necessary for their job, strict access restrictions should be implemented in tandem with adherence to the least privilege principle. Regularly review and update access permissions.
- Develop and disseminate an incident response plan that describes what should be done in this instance of security. Make sure that employees are aware of the correct manner in which to report safety-related issues.
- Physical Security: Remind your employees to keep their devices safe and secure. This involves maintaining laptops safe, employing privacy screens to prevent inappropriate viewing, and staying away from leaving electronics alone in crowded environments.
- Remote Work Policy: Establish a thorough plan for working remotely that takes into account security needs, appropriate use of the company's assets, and steps to take while safeguarding personally identifiable information. Consistently communicate and begin implementing these policies.
- Frequent Security Audits: To find vulnerabilities and opportunities for enhancement, conduct periodic security audits and assessments. Monitoring access logs, networking configurations, and the general safety posture are all components of this.
Organizations can enhance the security of their remote work environments and more effectively protect sensitive data from cyber threats by putting these recommended procedures into effect. Robust measures for cybersecurity must include training, regular monitoring, and adaptation to ever-shifting security environments.
In conclusion, considering our increasingly digitized and networked society as a whole the significance of multi-factor authentication (MFA) cannot be overstated. Since cyber dangers are always growing, conventional usernames and passwords are unsuitable to appropriately safeguard personally identifiable information. MFA functions as a comprehensive defense mechanism by demanding users to independently validate their identity using multiple techniques. This supplementary safety measure greatly lowers the likelihood of illegal access to data. In addition to being strongly advised for individuals as well as companies navigating the world of digital media, multi-factor authentication, or MFA, becomes essential to protecting against expanding cyber threats. By highlighting the importance of multi-factor authentication, we open up possibilities to a more resilient and secure digital future.
Recent Stories
500k Customer Have
Build a stunning site today.
We help our clients succeed by creating brand identities.
Get a Quote