HTTPS Implementation and Importance
Using HTTPS is essential to ensure safe communication over the internet in the modern digital age, when online privacy and data security are top concerns. When data is encrypted between the user's internet browser and the webpage they are seeing, hostile manipulation and spying are avoided. We may shorten this to HTTPS, which stands for Hypertext Transfer Protocol Secure. More than merely encryption, HTTPS authentication makes sure users can communicate with a trusted website. It is impossible to underestimate the significance of employing HTTPS, especially in conjunction with the growing number of cyberthreats and the stricter regulations pertaining to privacy. It likewise protects important info like credit card numbers, passwords, and personal information, it additionally shows a dedication to security and privacy. The beginning of this article establishes an environment for a comprehensive examination of HTTPS implementation by summarizing the significance of the standard and the recommended techniques for implementing it into the development of the website.
What is HTTPS?
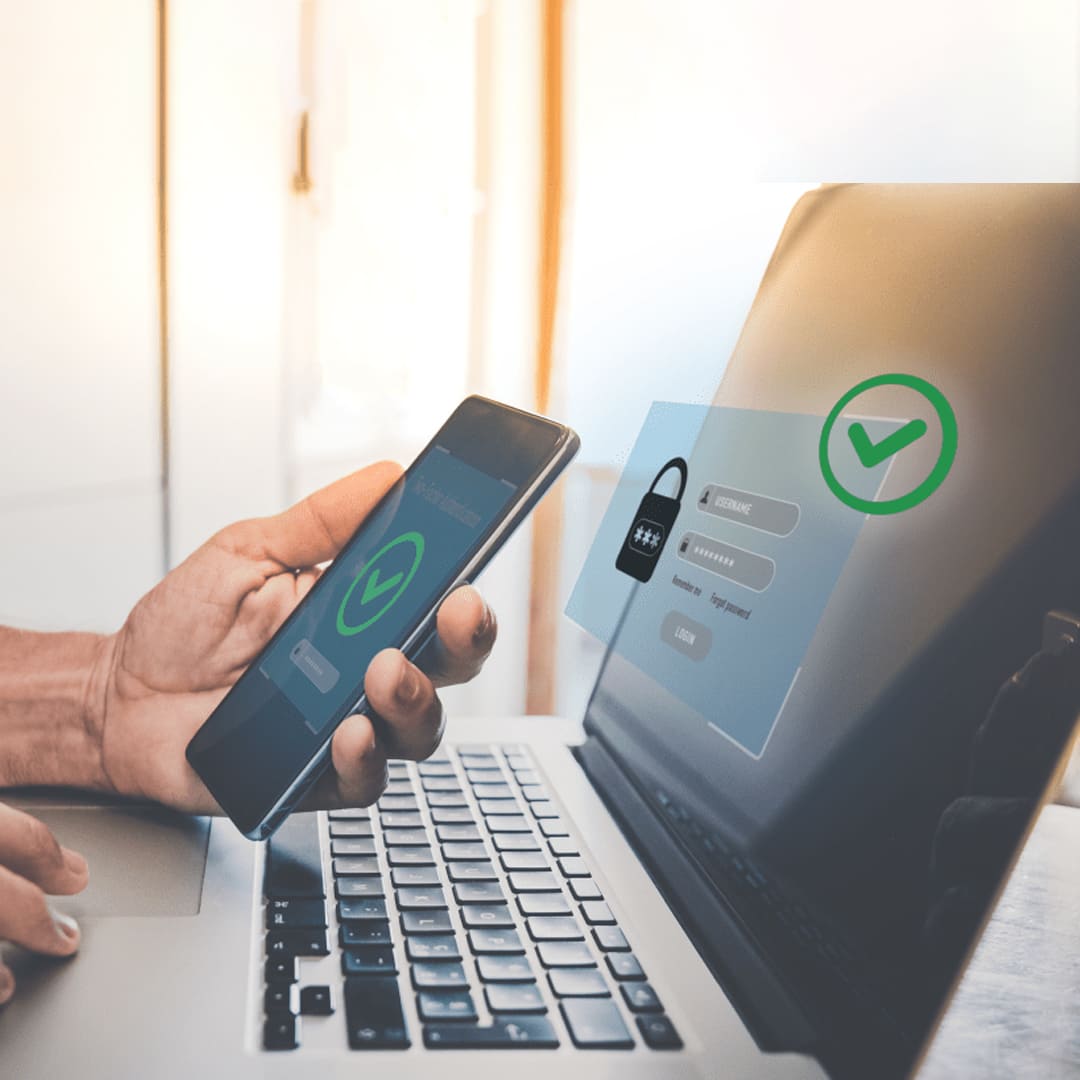
HTTPS is the rules and regulations used for secure hypertext transfer. It has been attempted to further develop the HTTP (Hypertext Transfer Protocol) by offering secure communication across a computer network, which is most frequently the internet. To stop unauthorized parties from copying, altering, or listening in on private information, HTTPS encrypts data as it is transferred between a user's web browser and the website server.
HTTPS has enabled authentication in addition to encryption, ensuring that visitors are communicating with the legitimate website and not a fake one. This authentication is carried out by computerized certificates, which confirm the trustworthiness of the website. Reliable Certificate Authorities (CAs) are the original providers of these certifications. Implementing HTTPS has become of greater significance than ever for website administrators and proprietors since it safeguards user confidentiality and security while also encouraging visitor confidence and credibility. Many contemporary web browsers alert users of possible security hazards when they visit websites that do not employ HTTPS. Because of this, using HTTPS to secure web connections has become standard procedure.
How HTTPS Works
The HTTP procedure, which serves as the means for transmitting data between a website's server and a web browser, has been combined with the SSL or TLS encryption (Secure Sockets Layer/Transport Layer Security) technologies in order to produce HTTPS (Hypertext send Protocol Secure). An overview of HTTPS's operation is provided below in simple form:
- Client Establishes Connection: A user's web browser starts a conversation with the web server that hosts the page when they enter the URL (Uniform Resource Locator) of the desired website.
- Client Validation: The web browser verifies that the SSL certificate is legally binding. It validates that the digital certificate matches the internet address of the website that is being accessed, is issued by an approved CA, and is currently valid. The browser establishes the connection if the digital certificate satisfies these inspections.
- Key Exchange: The internet browser generates a separate session key and encrypts it utilizing the public key of the website's server that it obtained through the SSL certificate. Information will be encrypted and decoded employing the current session key during communication between the internet browser and the website's server.
- The browser and server can now communicate securely when the session key has been set up. Every single one of the data that gets transmitted between them, including requests and responses made via HTTP, is encrypted using symmetrical data encryption algorithm design. Encryption renders any information unreadable by people who are not authorized, even in the uncommon scenario that it is captured.
- Session Termination: When an individual quits their internet browser or exits a website, the conversation between them comes to a sudden end. To prevent its reuse for more sessions, the session key is disposed of.
HTTPS Implementation's Significance
For a number of reasons, HTTPS (Hypertext Transfer Protocol Secure) installation is essential. These include:
- Data security: Through the use of encryption, HTTPS increases the difficulty with which hackers can intercept and decrypt sensitive information as it moves between a user's browser and the web server. This encryption is especially important for the protection of financial data, sensitive information, and user passwords.
- Protection of Privacy: HTTPS keeps user privacy protected by limiting illegal access to the content of communications between the browser and the server. It guarantees that users can browse the internet without fear of easy monitoring or tracking by outside parties.
- Users perceive websites that make use of HTTPS as reliable and trustworthy. The address window of the browser often presents an image of a padlock when the encryption protocol HTTPS is enabled, notifying visitors to the secured nature of the connection they are making to the website. This encourages user interaction with the website's content as well as increases the confidence of consumers in the website's reliability.
- Benefits of SEO: Google and other search engines favor secure websites higher in their results pages. By using HTTPS, a website's search engine rating can be raised, which will increase traffic and visibility. Websites that support HTTPS may appear higher in search results than websites that are not secure, as Google has said explicitly. HTTPS is a ranking indicator.
- Prevention Against Malware Injection and Man-in-the-Middle Attacks: HTTPS attempts to prevent malicious parties from interfering with or injecting malware into websites during the time they transmit information through the communication between the client and the website's server. Additionally, it minimizes the likelihood of attacks known as man-in-the-middle attacks, in which a computer programmer quietly records and changes communications between the two parties in question.
- Regulations: Complying with data protection regulations frequently necessitates encrypting sensitive data. Operators of websites can utilize HTTPS to abide by these legal requirements and prevent fines for noncompliance.
Challenges and Considerations for the Future
There are several difficulties and things to keep in mind when using HTTPS, such as:
- Administration of Certifications: Especially for websites with several subdomains or domains, SSL/TLS certificate management can be difficult. It includes configuring servers to use the appropriate certificates, obtaining certificates from trustworthy Certificate Authorities (CAs), and updating certificates prior to their expiration.
- Impact on speed: The additional processing power needed for HTTPS encryption and decryption may cause a little performance hit when using plain HTTP. The advantages of security, however, typically exceed the performance effect, and this expense has been reduced by improvements in hardware and encryption techniques.
- Mixed Content: Ensuring that all resources (scripts, stylesheets, and images) load safely during the HTTP to HTTPS conversion can be challenging. Should some resources continue to load over HTTP, mixed content warnings could appear, thereby jeopardizing the page's security. Website owners need to audit their content and update any insecure resource links to use HTTPS.
- Compatibility and Browser Support: While modern web browsers fully support HTTPS, ensuring compatibility with older browsers and devices is essential, particularly if a significant portion of the user base relies on outdated technology.
This may involve configuring servers to support older SSL/TLS protocol versions or employing fallback mechanisms for compatibility.
- Content Delivery Networks (CDNs): Adopting HTTPS may present additional difficulties for websites that rely on CDNs for content delivery. For secure communication to continue between the origin server and the CDN edge servers, it is essential to confirm that the CDN supports HTTPS and to configure SSL/TLS settings appropriately.
- Though switching to HTTPS can have SEO advantages, there is a chance that incorrect installation or configuration will cause short-term swings in search engine results. Owners of websites need to move traffic from HTTP to HTTPS with caution, update internal links and sitemaps with the new URLs, and use 301 redirects.
- Cost considerations: While extensive validation (EV) and wildcards are common features of free SSL/TLS certificates from Let's Encrypt and other comparable initiatives, more advanced certificates may cost extra. Platforms or services for managing SSL/TLS certificates may also have additional charges.
- Third-Party Integration: Making the switch to HTTPS may cause compatibility problems for websites that depend on third-party services or APIs. Ensuring that all third-party resources support HTTPS and updating integration configurations accordingly is essential for maintaining functionality and security.
- To overcome these obstacles and guarantee a seamless transfer to HTTPS while preserving the website's security and functionality, meticulous preparation, technical know-how, and continuing maintenance are needed.
Securing User Data in Web Applications
Securing user data in web applications is a critical aspect of maintaining trust, compliance, and overall security. The following are some difficulties and things to think about in order to achieve this:
- Data Encryption: Using sophisticated encryption techniques like HTTPS, protect data transferred across the user's browser and a website server. Ensure that powerful encryption techniques have been implemented for safeguarding sensitive data stored within databases or different types of storage to prevent unintentional disclosure.
- Authorization and authentication: Verify that users have been granted permission before providing them access to personally identifiable information by putting reliable authentication procedures in position, such multi-factor authentication (MFA). Use precise authorization criteria for controlling access to data depending on user characteristics and permissions in order minimize the possibility of unauthorized access.
- By carefully verifying and cleaning all user input, two common security vulnerabilities—cross-site scripting (XSS) and SQL injection attacks—can be prevented. While sanitization eliminates potentially harmful items from user input, input validation guarantees that only expected data forms are allowed.
- Follow secure code methods, like using parameterized queries for database access, to reduce common vulnerabilities. This will help ensure secure development procedures. To find and fix security vulnerabilities early in the development lifecycle, do routine code reviews and security assessments.
- Data minimization: Only gather and hold onto the bare minimum of user information required to ensure the functionality of the program. To lessen the possible impact of a data breach, institute data retention policies to remove obsolete or superfluous data and restrict access to sensitive data to those who are truly necessary.
- To prevent unwanted access to user accounts and session hijacking, enable session timeouts and sufficiently entropous session tokens. This is known as secure session management.
- To ensure that user actions are tracked, suspicious activity is identified, and security events are immediately addressed, it is recommended to implement effective logging and monitoring tools. To find and look into possible security breaches, keep an eye on error logs, security events, and access logs.
- When integrating third-party services and libraries into a web application, it is imperative to thoroughly evaluate their security posture and to follow compliance guidelines and best security practices. Regularly patching and updating external components helps reduce vulnerabilities found and reduce the chance of exploitation.
- It is crucial to understand and abide by relevant data protection legislation in order to ensure the secure processing and preservation of user data. Observe the law by implementing appropriate data protection and privacy measures.
- To effectively respond to security incidents and data breaches, create and update an incident response strategy on a regular basis. To reduce user impact and protect reputation, establish protocols for incident identification, containment, notification, and recovery.
Web application developers can improve the security posture of their programs and better shield user data from exposure, exploitation, and unauthorized access by bearing these issues and problems in mind.
All things considered, enforcing the validity, integrity, and privacy of data transmitted over the internet requires the use of HTTPS. To reduce the possibility of hackers, eavesdropping, and impersonation, HTTPS encrypts connections and verifies websites. This increases user confidence and trust in online meetings. The need to deploy HTTPS is becoming more and more critical as privacy concerns and cyber dangers develop. In order to preserve the security and privacy of their customers' sensitive data, web developers and organizations need to acknowledge HTTPS not just as a security precaution but as a standard need. Developers may help create a safer and more secure online environment where consumers can interact with confidence, knowing that their data is shielded from malicious exploitation, by making HTTPS a priority for all web domains and following best practices in its deployment.
Recent Stories
500k Customer Have
Build a stunning site today.
We help our clients succeed by creating brand identities.
Get a Quote