Security Best Practices in Web Development

Data breaches can be extremely harmful in today's society, where cyber threats are commonplace. Security is therefore essential to web development. The most secure procedures have been used in the development of dependable and trustworthy online apps. For developers and businesses alike, security is crucial, whether it's to safeguard private user data, fend off hostile assaults, or stay in compliance with strict rules. Strengthening the dependability and resilience of web-based systems requires the implementation of established security rules. This consists of putting robust authorization mechanisms in place, implementing encryption techniques, and improving software on an ongoing basis. In order to create and maintain secure digital environments, this introduction lays the groundwork for a thorough examination of security best practices in web development. It covers important tactics and approaches.
HTTPS Implementation and Importance
Data can be sent with an additional layer of security by a user's browser and the website they are watching by using the HTTPS (Hypertext Transfer Protocol Secure) version of HTTP. By avoiding manipulation or interception, encryption improves data security during transmission. Here's why HTTPS implementation is important:
- Data security: Information is protected by encryption during transmission throughout HTTPS between the browser used by the user and a website server, avoiding data interception even in the unlikely possibility that it is intercepted by unidentified individuals. This is especially significant for sensitive data, such as usernames and passwords for credit cards, and other sensitive information.
- Communication with the intended website is ensured, and a malevolent imposter is avoided, thanks to HTTPS's authentication feature. It verifies the webpage's identity by using digital certificates issued by respectable Certificate Authorities (CAs).
- Users consider websites that are encrypted by HTTPS to be more dependable and trustworthy. The padlock symbol and "https://" in the URL convince users that their communications with the website are private.
- One benefit of SEO is that HTTPS websites rank higher in search results from search engines like Google. As a mark of trust and security, they claim that HTTPS enhances a website's visibility and traffic.
- Attack Prevention using Man-in-the-Middle (MITM): Without HTTPS, information sent between a user as well as a website is vulnerable to hacker interception. Due to HTTPS encryption, which guarantees end-to-end data encryption, several types of attacks are avoided.
- Encrypting data with HTTPS prevents unauthorized parties from altering or tampering with the information sent back and forth between a website and its users, providing data integrity.
- Future-proofing: HTTPS gives users and website owners a strong foundation for security as security threats change and technology progresses. By using HTTPS right once, websites can be strengthened against emerging security risks.
In conclusion, HTTPS is essential for safeguarding private user information, preserving confidence, adhering to legal requirements, and outpacing security risks. It is an essential component of modern web security and should be implemented by all websites that handle sensitive information or prioritize user trust and security.
Securing User Data in Web Applications
In order to preserve user confidence, adhere to legal requirements, and guard against data breaches, online applications must securely store user data. In order to secure user data in online applications, take into account these four crucial steps:
- Employ HTTPS: By using HTTPS, you may encrypt user and web application data as it is transmitted. This guarantee guards against data modification and eavesdropping during network transfers.
- Input validation is necessary to prevent common security vulnerabilities. Make sure that all customer input is validated. Before processing the data, use server-side validation to guarantee its integrity.
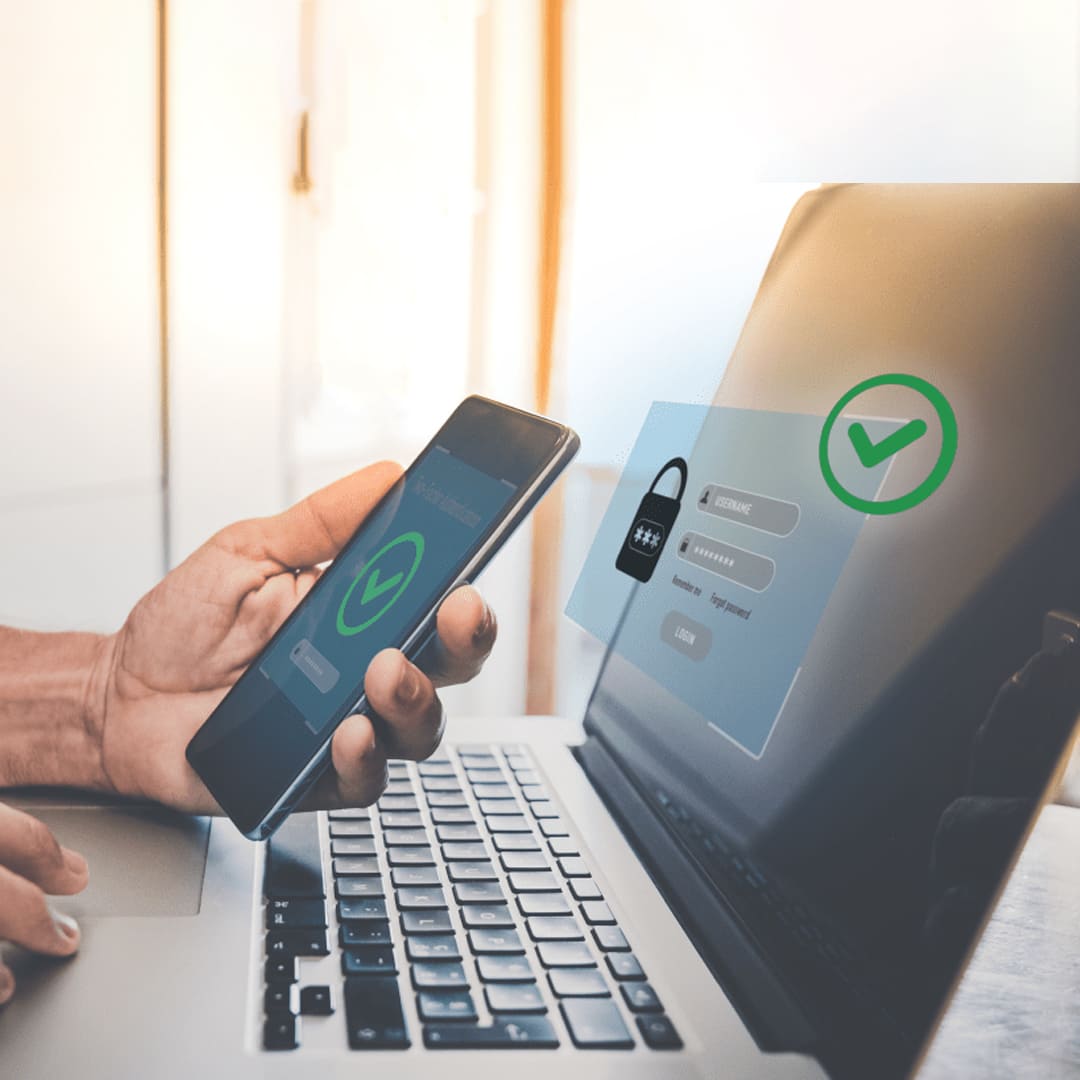
- Authorization and Authentication: To confirm the legitimacy of people using your online application, put strong authentication procedures in place. If you want extra protection, think about implementing multi-factor authentication (MFA) or using powerful password hashing techniques. To further limit users' access to only the resources they are permitted to access, implement appropriate authorization restrictions.
- Data Encryption: Use robust encryption algorithms to encrypt critical user data while it is at rest. This covers any sensitive data kept in files or databases, including passwords and personally identifiable information (PII). Make use of key management procedures and industry-standard encryption mechanisms.
- Enact secure session management procedures to safeguard session identifiers and thwart attempts to hijack sessions. To reduce the possibility of session-related vulnerabilities, use secure cookies with the relevant properties, such as "HttpOnly" and "Secure" flags.
- Least Privilege Principle: Restrict user, process, and system access permissions to the absolute minimum required to carry out their intended functions. Restricting entry aids in lessening the possible effects of illegal entry and security breaches.
- User inputs, logs, error messages, and other outputs that are displayed to users should all have sensitive information removed or obscured. To do this, apply data sanitization and redaction procedures. Reduce how often unauthorized parties see sensitive data.
- Follow best practices and standards for secure coding throughout the software development lifecycle. Automate security testing tools, do code reviews, educate engineers on secure coding standards, and identify and address security problems early in the development process.
- Develop and maintain an incident response strategy to guarantee that security lapses and problems are resolved efficiently. Establish processes to recognize, contain, and address security vulnerabilities. Follow applicable requirements when alerting parties of the occurrences.
Web applications can enhance user data protection, reduce security risks, and comply with privacy rules by putting certain security measures into place. To handle new threats and weaknesses, security must be continuously monitored, updated, and improved.
Common Web Security Vulnerabilities
Web applications or systems that have security flaws that an attacker could use to jeopardize the availability, confidentiality, or integrity of data are known as open vulnerabilities. Common web security flaws include the following:
1.Injection Attacks:
- By using faulty input validation and SQL Injection (SQLi), attackers can execute unauthorized database commands and insert malicious SQL queries through input fields.
- Attackers can cause unapproved actions or data theft by inserting malicious scripts, typically JavaScript, onto web pages that other users are viewing. This technique is known as cross-site scripting (XSS).
2.Broken Authentication:
- Weak Passwords: People select passwords that are simple to figure out or break, giving hackers access to user accounts without authorization.
- Several issues with session management can lead to unauthorized access to user sessions.
3.Sensitive Data Exposure to Insecure Transmission:
- Sensitive information is vulnerable to interception by nefarious actors when it is sent via unencrypted channels.
- Insufficient information encryption leaves sensitive data susceptible to theft in the event that the core storage system is breached.
4.An XML foreign Entity (XXE) attack is the process of incorporating foreign entities using XML parsers that aren't very strong. Denial-of-service (DoS) attacks, server-side request forgery (SSRF), or unauthorized access to private data could arise through this.
5.Broken Access Control:
- Using object references in URLs to obtain illegal access to data or functionality is known as Insecure Direct Object References, or IDOR.
- Not Enough Authorization Checks Not enforcing appropriate authorization rules, including least privilege principles or role-based access control (RBAC), which permits unauthorized users to access resources that are forbidden.
6.Security Misconfigurations:
- Default Credentials: Using default or weak credentials for system components, administrative interfaces, or third-party services.
- Resources that are exposed to unauthorized access are those that have security settings, server settings, or directory permissions incorrectly set up. These include sensitive files and directories.
7.Cross-Site Request Forgery, or CSRF, is a method of doing inappropriate things on behalf of an individual using authenticated sessions with users. Usually,
fraudsters accomplish this by tricking the user into completing out forms or clicking on links that were intentionally created unconstitutionally.
8.Using vulnerabilities in deserialization techniques to run arbitrary code, alter data, or initiate denial-of-service attacks is known as "insecure deserialization."
9.Leveraging Outdated or Vulnerable Frameworks, Libraries, or Third-Party Components: Web applications which utilize the references to these elements expose themselves to the possibility of allowing harmful programs to execute or unauthorized access to the computer's infrastructure.
Addressing these issues requires a comprehensive web application security approach. This includes doing frequent security audits, using safe coding techniques, managing configurations correctly, and providing continuous monitoring and updates.
Strategies for Regular Security Audits and Updates
To keep online applications secure and intact, regular security assessments and updates are essential. Here are strategies to effectively conduct security audits and implement updates:
- Establish a Timetable: Make arrangements to perform routine updates to safety measures and audits. This could take place regularly, on a quarterly basis or semi-annually, depending on the complexity of the application you are developing, the amount of frequency of developments, and the necessary amount of security.
- Establish Goals and Scope: Clearly state the goals and scope of every security audit. Determine the parts of the web application that need to be audited, including the network architecture, databases, server configurations, coding, and third-party integrations. Establish the precise security objectives and areas of concentration, such as finding security flaws, making sure security standards are followed, or evaluating how well security controls are working.
- The process of performing security audits involves the selection of suitable instruments and methods, which should be determined by the objectives and extent of the audits. Frameworks for penetration testing, code analysis tools, automatic vulnerability scanners, and manual security inspections may all fall under this category. In order to thoroughly evaluate the web application's security posture, employ a variety of techniques and tools.
- In order to detect any security flaws or possible hazards, thoroughly assess the web application's vulnerabilities. Take a look at any common weaknesses in your system. Look for common weaknesses in your system. Arrange vulnerabilities in order of severity and possible influence on the security of the application.
- Testing for vulnerabilities: Also referred to as pen testing, penetration testing is an approach for simulating real-world assaults and assessing the extent to which security controls work. When weaknesses are found throughout the vulnerability assessment process, specialists in security or the field of ethical hacking should be contacted. Penetration testing tests the online application's resistance to sophisticated attacks, finds security control gaps, and validates the impact of vulnerabilities.
- Find coding errors, incorrect configurations, and security vulnerabilities in the web application by doing code reviews and configuration audits. Examine the source code, third-party libraries, server configurations, database schemas, and source code for vulnerabilities and adherence to secure coding practices. Make sure security elements including access controls, output encoding, authentication, and input validation are applied correctly.
- Remain Up to Date: Stay up to date on new security hazards, vulnerabilities, and web application security standards of excellence. To keep apprised of the most recent security trends and warnings, subscribe to professional publications, forums, and lists of communication for security. By paying attention to security-related groups, open-source initiatives, and software vendors' alerts, you may keep a watch out for future updates and patches that address vulnerabilities that have been found.
- Record Findings and remedial: Record the results of security audits, together with the vulnerabilities that were found, how serious they were, and remedial suggestions. Based on the degree of risk, rank vulnerabilities in order of importance and create a remediation strategy for each problem that is found. To successfully mitigate security threats, implement remedial steps, such as updating software components, applying patches, changing configurations, or altering code.
- Test Updates in Staging Environment: Before deploying updates to the production environment, test them thoroughly in a staging or testing environment. Verify that updates do not introduce new vulnerabilities or disrupt the functionality of the web application. Perform regression testing to ensure that existing features remain intact and functional after applying updates.
- Continuous monitoring systems should be enabled in order to monitor security and quickly detect and address security incidents. Employ intrusion detection systems (IDS), security intelligence and event management (SIEM) remedies, and log analysis tools to keep an eye on any unusual activity, unauthorized access attempts, and the possibility of security breaches. Security controls, regulations, and procedures have to be regularly examined and revised in order to maintain an anticipatory approach to security and the flexibility for dealing with potential hazards.
Organizations may efficiently detect and reduce security threats, bolster the security of their online applications, and protect sensitive data from unwanted access and exploitation by using these procedures for routine security audits and updates.
To sum up, in order to reduce risks and protect important assets, web developers must pay constant attention to security best practices. Since cyberattacks get more sophisticated and technology evolves, developers must always be searching for new ways to fortify web programs against vulnerabilities. Developers can increase system resilience and reassure consumers about data safety by adhering to established security standards, which include doing rigorous code reviews, maintaining continuous monitoring, and taking proactive actions to limit threats. Encouraging an organizational culture that prioritizes security is also essential to guaranteeing that all pertinent parties understand the need for security to be a top concern during the whole development process. By integrating robust security measures into every facet of web development, developers may ultimately create digital ecosystems that are safe, resilient against evolving cyberthreats, and valuable and functional as well.
Recent Stories
500k Customer Have
Build a stunning site today.
We help our clients succeed by creating brand identities.
Get a Quote